THE 1-SECOND SHIELD: WHY EVERY AI BUILDER NEEDS PACKET-LEVEL DDOS PROTECTION
Picture this: your high-performance inference engine is finally scaling, users are pouring in, and your GPU clusters are humming—until they aren't. Suddenl...
The 1-Second Threshold: Why Your AI Infrastructure is Currently a Sitting Duck
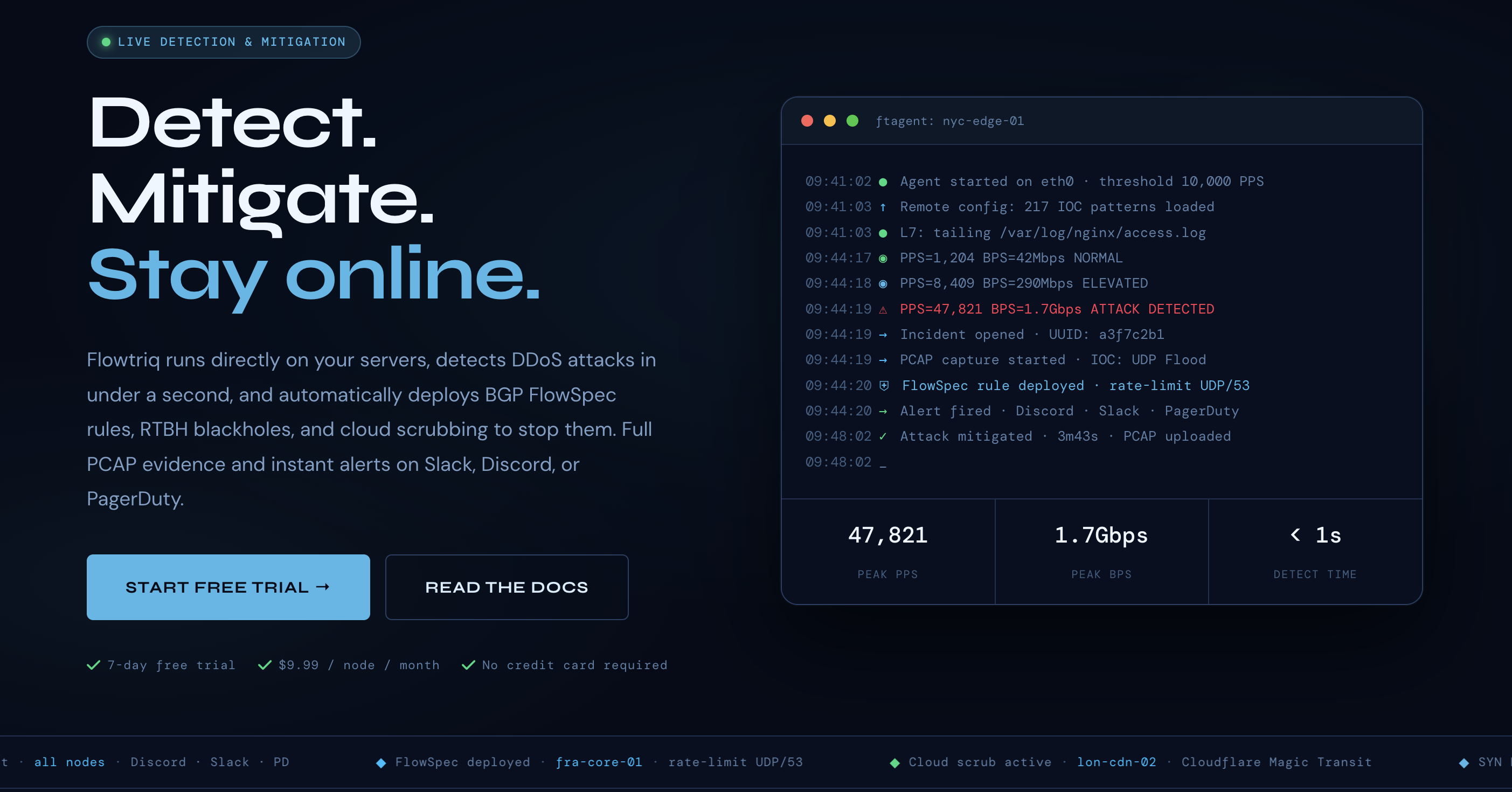
Picture this: your high-performance inference engine is finally scaling, users are pouring in, and your GPU clusters are humming—until they aren't. Suddenly, latency spikes, your API calls time out, and your Slack starts blowing up with "is the site down?" messages while your compute costs continue to bleed. Flowtriq is a lightweight, agent-based DDoS detection and auto-mitigation platform that stops these outages in under one second. For AI leaders, it matters because it turns a potential weekend-killing catastrophe into a silent, automated non-event. The bottom line: if you aren't protecting your endpoints at the packet level, you're leaving your uptime to chance.
The Business Case: Uptime as a Competitive Moat
In the world of AI, latency is the silent killer of user retention. We spend months optimizing model weights and quantization just to shave off 50ms of token generation time, yet many solo builders and mid-sized firms leave their front door wide open to volumetric attacks that can paralyze an entire stack. Flowtriq shifts the paradigm from reactive firefighting to proactive, algorithmic defense.
From a market positioning standpoint, integrating a tool like Flowtriq allows you to offer "Enterprise-Grade Availability" without the enterprise-grade overhead. By automating the detection of over 8+ attack types—including the nasty Mirai botnet variants—you effectively remove the need for a 24/7 on-call network security team. For a solo builder or a lean startup, this is pure leverage. You’re not just buying a security tool; you’re buying back the focus required to actually build your product. In my experience, the $9.99 per node price point is almost an insult to the traditional "Big Tech" security vendors who charge five figures for similar sub-second mitigation capabilities. It’s a democratization of infrastructure resilience.
High-Level Strategic Benefits
- ▸Operational Efficiency: Flowtriq eliminates the "war room" culture. By using ftagent to learn normal traffic baselines and auto-deploying BGP FlowSpec rules or cloud scrubbing (like Cloudflare Magic Transit or Hetzner) within one second, your team stays focused on shipping code rather than analyzing packet captures during an incident.
- ▸Cost Impact: The flat-rate pricing model is a massive win for budget predictability. Unlike many "cloud-native" firewalls that hit you with "data processed" surcharges during an actual attack—effectively taxing you for being a victim—Flowtriq’s fixed cost ensures your margins stay intact even under heavy fire.
- ▸Scalability: As you move from a single inference server to a distributed edge network, Flowtriq scales with you. Its multi-node management dashboard allows you to push unified mitigation playbooks across your entire fleet, ensuring consistent security posture regardless of where your compute lives.
- ▸Risk Factors: While the "set it and forget it" nature is appealing, leaders must ensure that escalation policies are correctly mapped to their specific provider’s capabilities (e.g., ensuring BGP hooks are supported). Additionally, while the sub-second detection is world-class, Layer 7 "low and slow" attacks still require thoughtful baseline tuning to avoid false positives during legitimate viral traffic spikes.
Implementation Considerations: From Zero to Protected in Minutes
If there’s one thing I hate, it’s a security tool that requires a six-month professional services engagement. Flowtriq is the antithesis of that bloat. The implementation is a "copy-paste" affair: a Python-based agent that installs on Linux in under two minutes. This is critical for AI builders who are often iterating on their infrastructure weekly.
The real strategic work lies in the Automation Runbooks. You’ll need to decide your escalation path: do you want to simply drop packets at the edge, or trigger a full cloud scrub? Because Flowtriq triggers an automatic PCAP (packet capture) for every attack, your post-mortem analysis becomes data-driven rather than speculative. Integration-wise, it plugs directly into the tools your team already uses—Discord, Slack, and PagerDuty—ensuring that while the mitigation is automatic, the visibility remains absolute. This isn't just a technical install; it's a shift toward an "immutable audit" culture where every network anomaly is logged and classified without human intervention.
The Security Landscape: Cutting Through the Noise
When evaluating Flowtriq, you have to look at the incumbents. Traditional players like Akamai or Cloudflare offer robust protection, but they often act as a "black box" where you have little visibility into the raw packet data unless you're on a massive Enterprise contract. On the other end, DIY solutions using iptables or basic fail2ban scripts are simply too slow and brittle for modern multi-vector attacks.
Flowtriq sits in the "Goldilocks zone." It provides the granular control of a custom-built solution with the "push-button" ease of a SaaS. While AWS Shield is great if you are locked into the Amazon ecosystem, Flowtriq offers a provider-agnostic layer that is essential for builders running multi-cloud or hybrid-edge setups. Its original research, including the Mirai botnet kill switch (CVE-2024-45163), gives it a level of "street cred" that many generic security startups lack.
Recommendation: The Path to Infrastructure Immunity
Stop treating DDoS protection as a "nice-to-have" for later. If your AI service is accessible via a public IP, you are already a target. I recommend a three-step rollout:
- ▸Deploy the 7-day trial on your most exposed edge node today—it takes two minutes and no credit card.
- ▸Audit your baseline traffic for 48 hours to let the agent learn your "normal."
- ▸Configure a Slack webhook and a basic RTBH (Remote Triggered Black Hole) policy to automate your first line of defense.
One builder. One AI. Zero downtime. That's the goal.
OBJECTIVE TARGET:
FLOWTRIQ